
Remote Worker Security on ANY Unmanaged or Personal Device Without VDI
Venn’s Secure Enclave allows workers to safely access work apps and files on their own devices. Removing the burden of buying/shipping laptops or dealing with costly virtual desktops.
See how Venn enables remote access security for BYOD and protects company data on personal devices (without the cost & latency of virtual desktops!)
Your time is precious! That’s why we’ll get right to business if you book time with us.
Items we’ll cover with you include:
We’ve scrapped multiple discovery calls to get right into business. You’ll meet directly with our Remote Work Security Expert.

Schedule Your Demo
Trusted By:

Introducing
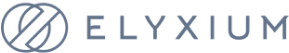
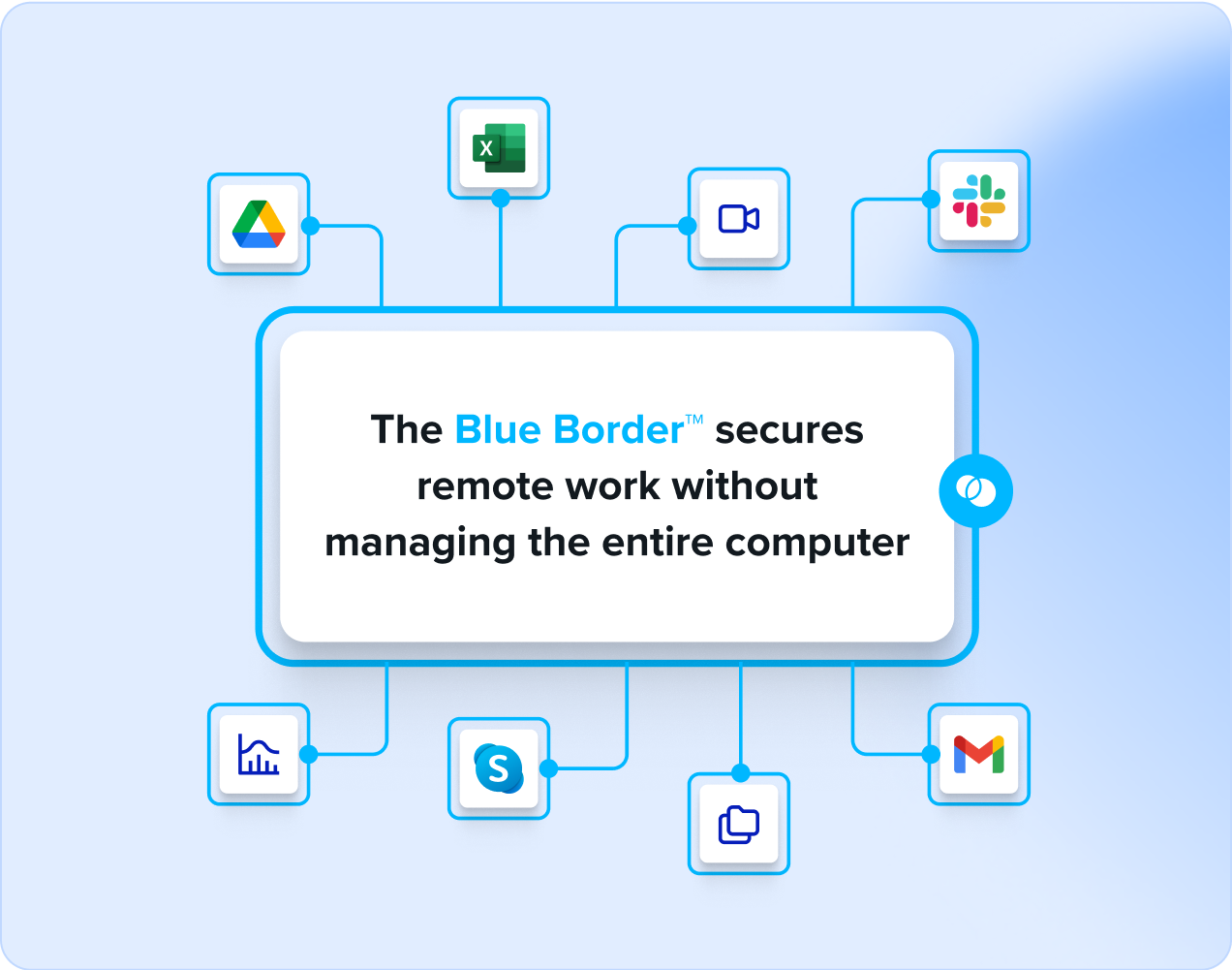
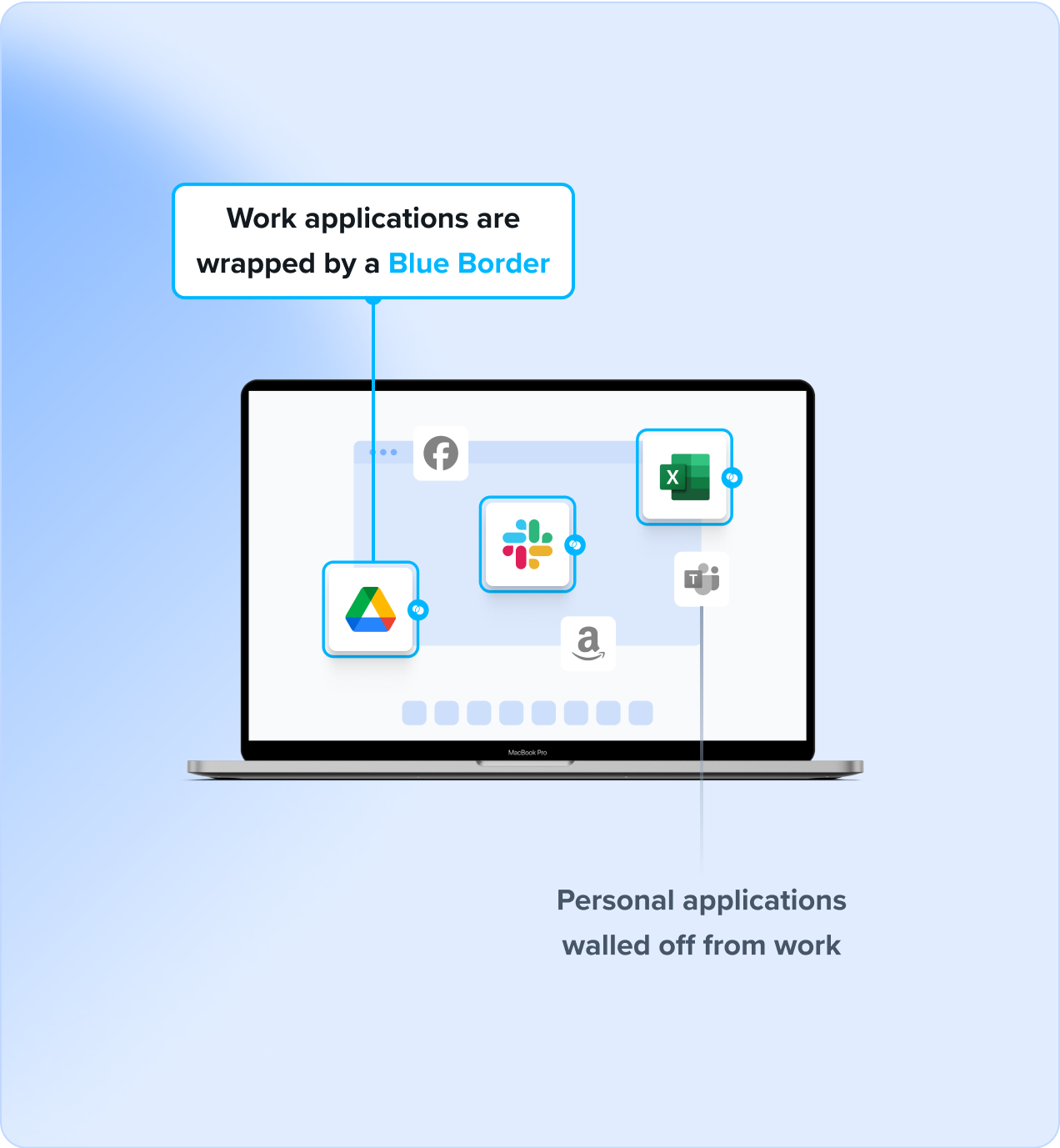
Venn’s Blue Border™ protects company data and applications on BYOD computers used by contractors and remote employees. Similar to an MDM solution but for laptops – work lives in a company-controlled Secure Enclave installed on the user’s PC or Mac, where all data is encrypted and access is managed. Work applications run locally within the Enclave – visually indicated by Venn’s Blue Border™ – protecting and isolating business activity while ensuring end-user privacy.
This is Venn – the Blue Border keeps your company-based apps, data and network safe and compliant. Venn secures remote work on any unmanaged or BYOD computer with a radically simplified and less costly solution than VDI.
- Centralizes administrative control over work data, application and peripheral use.
- Provides IT departments the robust control to remotely enable, suspend, terminate or wipe at press of a button. Onboard & offboard in minutes.
- Ensures that all network access is policy-controlled and guarded from accidental or malicious exfiltration, compromise or loss.
- Significantly cuts costs and makes remote work a walk in the park for IT teams and employees. No need for remotely delivered apps – everything runs locally on the employees computer.
How Venn Keeps Work Inside a Secure Enclave
Launch Venn’s app from any device
Venn Kicks in and automatically detects work apps
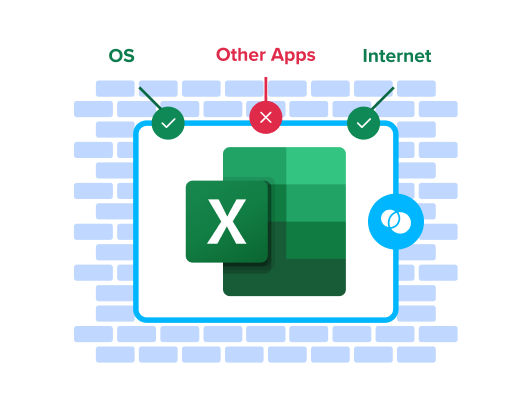
The blue border acts a firewall to safeguard work apps and data
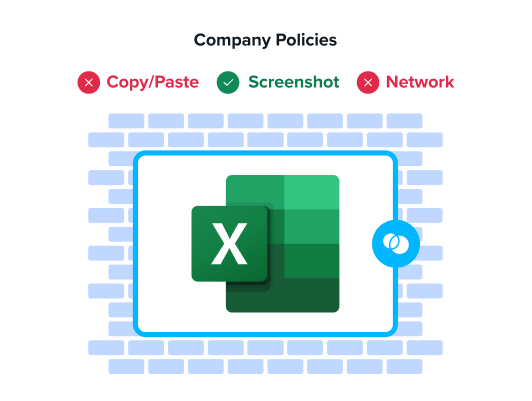
Work comfortably from any device with guaranteed compliance and regulations
BYOD Workforce
Secure unmanaged and BYOD on any PC or Mac.
Virtual Desktop Alternative
Eliminate complexity and reduce costs.
Zero Trust Security
Isolate and protect work data and applications.
MDM for Laptops
Control, Secure and Administer policies on any BYOD laptop.
Securing Contractors and Offshore Workers
Secure sensitive client assets and meet compliance.
Work & Personal on One Device
Control, Secure and Administer policies on any BYOD laptop.

If we can get rid of just a portion of our laptops a year, it basically pays for all Venn users.

By using Venn, we can leverage our time and talent to help our advisors to be more successful…

Venn is one of my favorite products to come in to the market. I think it will change things and drive the sun-setting of VDI, so to say, to start moving to this newer, more modern world of working from BYOD devices.

Venn is a great solution for any company with remote employees and contractors that have regulatory requirements or wants to reduce the cost of PC management.
Hop Onboard,
You’re in Good Company
Over 700 security and compliance-driven companies depend on Venn to empower their BYOD users.
Compliance with Industry Standards
Venn ensures compliance with all current cybersecurity regulations which require development and implementation of mandatory policies, principles, standards and guidelines.